The pandemic has drastically shifted our way of life. Businesses are still relying on online forums, and our world is more than ever dependent on the internet and online spaces. With this, privacy and security of sensitive information have become a major concern.
And it would be correct to say that this has been a long-existing one. With the debate on how our information has the ability to fall in anyone’s hand, the internet has become a vulnerable space.
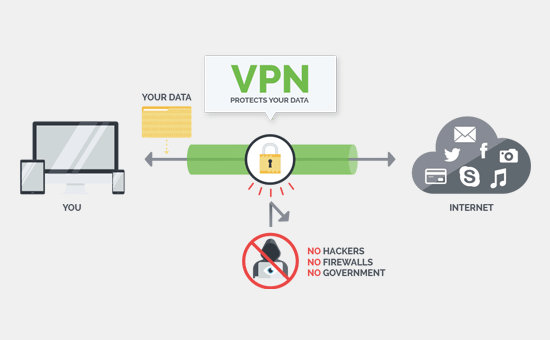
This is where Virtual Private Network (VPN) comes in handy against the numerous evil and prying forces across online spaces. So let’s first understand what is VPN and how it helps.
What is VPN?
A VPN could help you to maintain your privacy by simply creating an encrypted pathway between you and a remote server handled by a VPN operator.
It helps you remain anonymous by shadowing your Internet Protocol (IP) address. This means no one can trace your sensitive data virtually.
So, for example, if you use public wifi through a secure VPN, you will be far at less risk of getting your information exposed to any third-party users out there.
How does it work?
The tech-savvy talk has always been the boring side of the story. However, getting into the details might get interesting and help you remain informed in the highly vulnerable online space.
Let’s start with the tale of the internet itself. The Internet was created to transmit what we can call “packets” of data as efficiently as possible.
The idea mainly was to move data on the top of the Internet Protocol (IP), which sets the foundation of how these “packets” of data move from one end to the other.
In those early days, when the world far more innocent, the concern was to get data from one point to another without any special attention to security. So by design and origin, the Internet has never been safe.
If you have to make a quick purchase and you log into public wifi at a mall, the chances are that your information will be at risk. To help us avoid such risks, VPN plays its part.
A VPN encrypts your data requests at the originating point, keeping your information and IP address hidden.
It then sends it to a VPN server where the information is decrypted and then pushed to the public or website servers. This way, you could remotely be accessing any requested websites with your anonymity maintained and location untraced.
So it is like you need the candy in the kitchen but don’t want your siblings to know, so you take the back window. And your secret remains yours.
But, Why do I need a VPN?
The threats to security on the internet are uncontrollable; however, we can remain informed and use technology against technology itself.
Therefore, you need to have a good VPN software to have your sensitive data safe. Here are the reasons why you should have a VPN.
- Firstly, your data is secure, and you are untraceable. Everything moving from the origin to the VPN server and to the Public server follows a safe route with your information being at minimum risk.
- With certain sites being inaccessible in various regions, VPN allows us to surpass these limitations. It allows you access to these sites from a different geographical location.
- Public wifi is a serious threat. However, you might need it urgently anywhere, so accessing public internet through a VPN can help you avoid the risk.
- Love movies and online streaming? Then shield yourself against potential risky intermediaries on the torrenting or online websites through the use of a reliable VPN.
What are the types of VPN to look at?
There are multiple kinds of VPN that have different standards and the use of technologies. The following are the few of many that are known commonly.
- Point-to-Point Tunneling Protocol (PTTP): The VPN came about around the mid-1990s and is still widely used. The PPTP uses GRE protocol to enclose information.
As the technology itself doesn’t do encryption, its implementation has been questioned by tech-experts, especially the Microsoft Implementation version. It could potentially not be as secure.
- IPSec: A better version of PTTP, the VPN type has a range of protocols and use of technologies. The VPN has drawn significant attention due to its flexibility in the commercial sector.
However, the same flexibility has also been identified as a problem due to the protocols’ complexity. The technology has to be implemented with other measures to ensure effectiveness.
- Secure Shell (SSH): The protocol is performative of both tunneling and encryption in a VPN network. SSH is known to offer strong encryption and management access remotely.
Network operators use the technology for handling managing systems and applications remotely, implement commands and transfer files from one point to the other.
But how do I make the pick?
That has been an information load already. But after reading all this, you might be considering to get a VPN service to surf safely online. Even $1 VPN can ensure your online security. It is, therefore, the following basic tips that will help you make the right choice.
- Geography matters. The location of origin for your VPN service will help you get through regional limitations. So it’s important your VPN operates in the regions that you want to get access to.
- Where you will be using the VPN matters, you need to consider what devices will be in use to operate the VPN. So are you using a tablet, phone, or PC, you will have to identify a technology that will be compatible or dedicated to the interface you are using.
Here are a few free VPNs that you can potentially use.
- Hotspot Shield Free VPN
- Tunnel Bear
- PotonVPN Free
- Windscribe
- Speedify
- Hide.me
So if you are worried about your precious data online and how you can keep it secure, A good VPN could be your answer.
Happy Surfing!
Read Also



